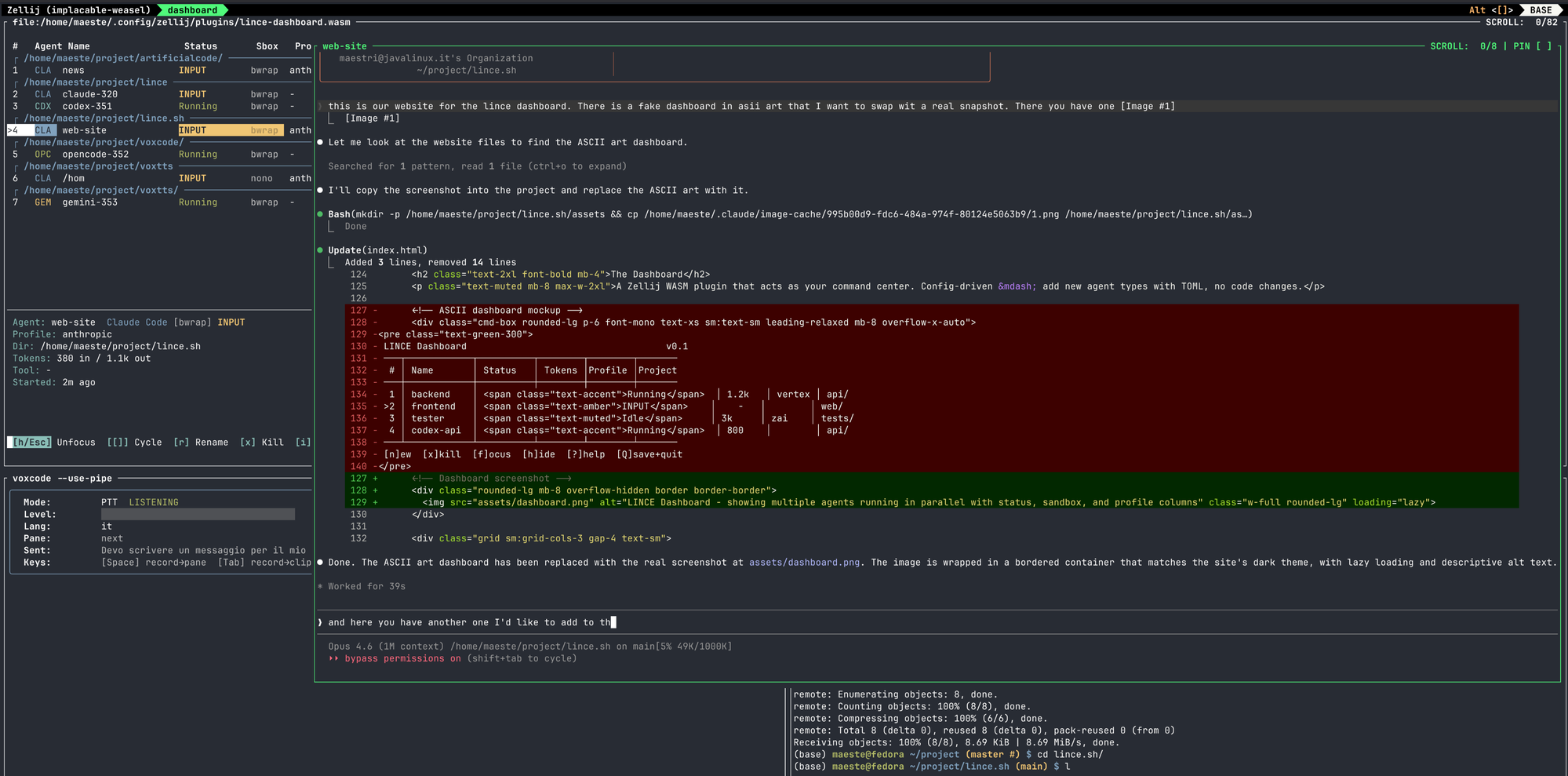
The Dashboard
A Zellij WASM plugin that acts as your command center. Config-driven — add new agent types with TOML, no code changes.
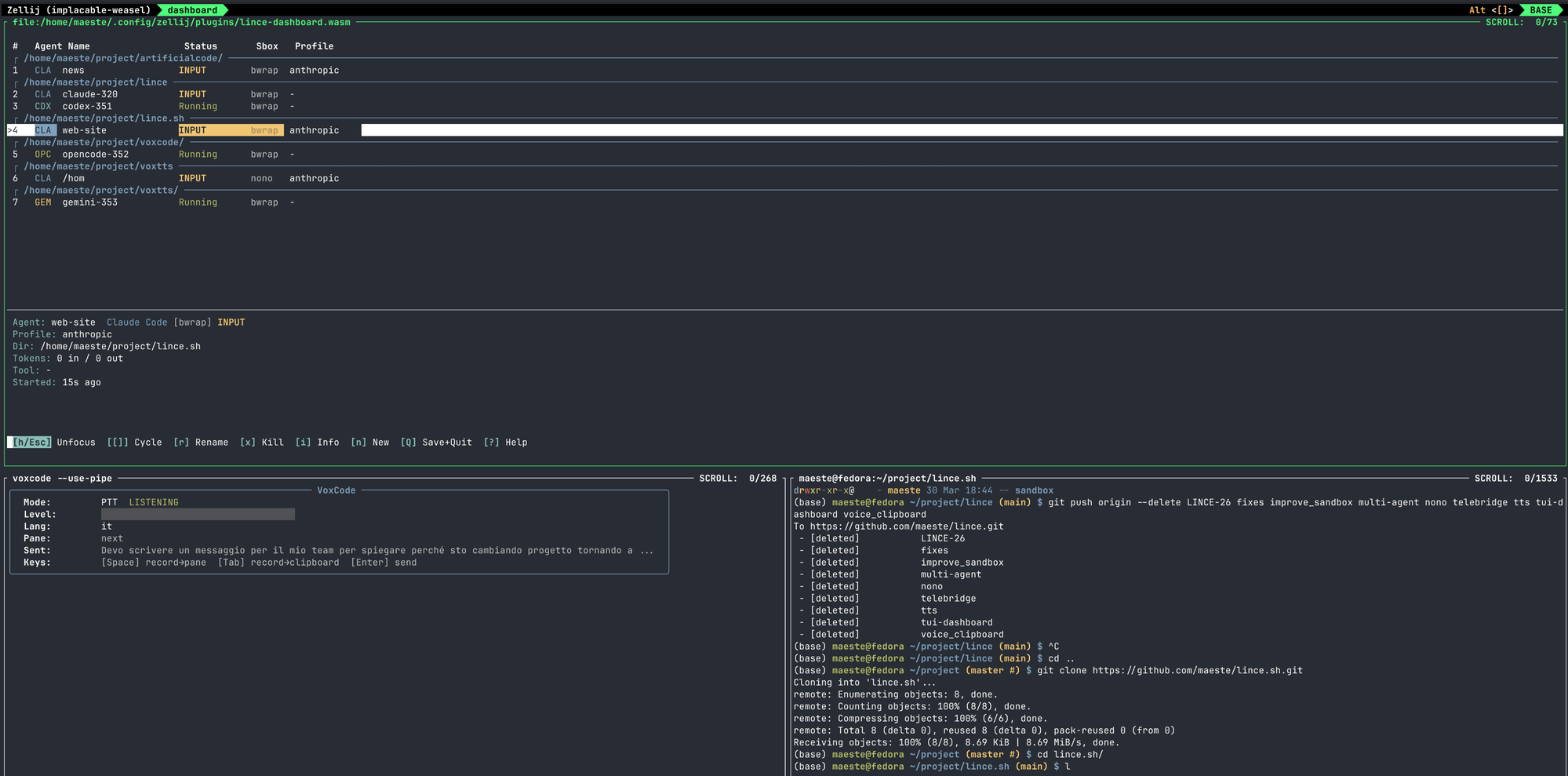
Multi-agent
Multiple agents in parallel. Claude, Codex, Gemini, OpenCode, or custom.
Session persistence
Save and restore your agent constellation across sessions.
Voice relay
VoxCode transcriptions piped directly to the focused agent.
Sandbox isolation
Choose a sandbox backend per agent at launch — or run unsandboxed when you need full host access.
Swimlane grouping
Agents auto-grouped by project directory when working across repos.
Config-driven
Add agents via TOML. No code changes, no recompilation.